

As the holiday season approaches, businesses often experience a shift in work patterns. Employees may travel, work remotely, or adjust…


As the 2024 holiday season approaches, the excitement of shopping and gift-giving is in the air. However, it's also a…


Tales of Cyber Disasters In the digital age, cyberattacks are becoming more frequent, sophisticated, and devastating. These horror stories often…


Social engineering attacks are some of the most effective tricks used by cybercriminals. By manipulating human emotions like trust, urgency,…


As we move deeper into 2024, now is the ideal time to review and optimize your IT budget. A well-planned…


As we approach the final quarter of the year, businesses across all industries often face a surge in activity. Whether…


As the new school year approaches, students and parents are gearing up for a fresh start. Technology plays a crucial…
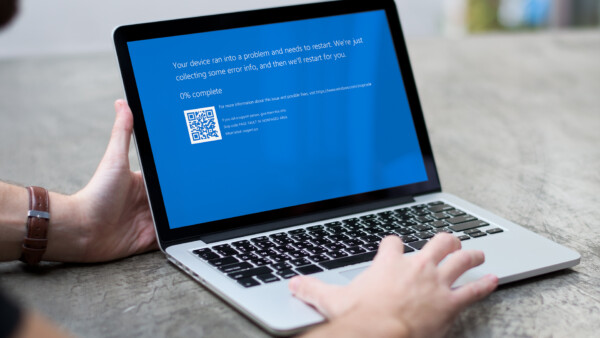
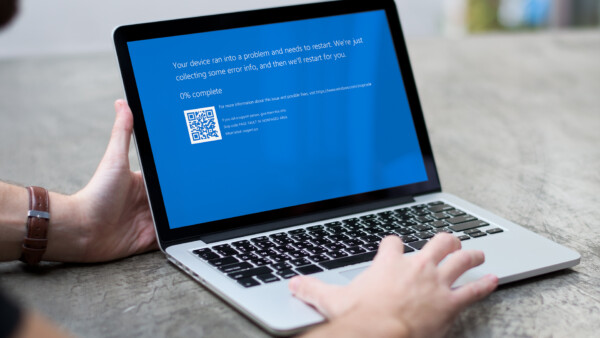
The recent CrowdStrike outage serves as a significant wake-up call for businesses relying on cybersecurity solutions. CrowdStrike's temporary service disruption,…


A new warning for Google Chrome users has emerged, carrying a critical yet straightforward piece of advice: avoid copying and…